Overview
Recently, cybersecurity researchers identified three malicious npm (Node.js package manager) packages targeting Cursor, a popular AI-driven code editor, specifically for macOS users. These packages have been downloaded over 3200 times in total.
According to Kirill Boychenko from Socket, a software supply chain security company, these packages masquerade as developer tools providing the “cheapest Cursor API” while stealing user credentials and fetching valid encrypted payloads from infrastructure controlled by threat actors. They overwrite Cursor’s main.js file and disable automatic updates to maintain persistence.
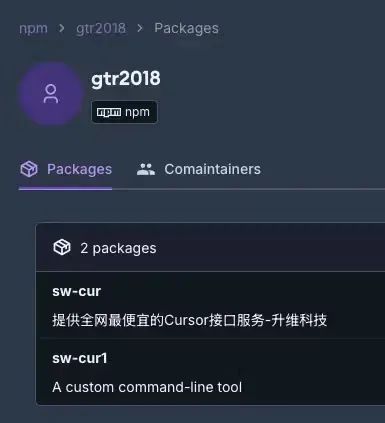
Malicious Packages
The problematic packages are:
- sw-cur (2,771 downloads)
- sw-cur1 (307 downloads)
- aiide-cur (163 downloads)
Notably, aiide-cur was first released on February 14 this year, uploaded by a user named “aiide,” described as a command-line tool for configuring the macOS version of the Cursor editor. The other two packages were released a day earlier by a malicious actor using the alias “gtr2018.”
Upon installation, these packages aim to obtain user-provided Cursor credentials and retrieve the next stage payload from remote servers (“t.sw2031[.]com” or “api.aiide[.]xyz”), replacing legitimate Cursor-specific code with malicious logic.
After analyzing the code snippets of these three packages, Socket discovered that they share a core backdoor logic: only the hardcoded domain names differ, while the credential theft, encrypted loader retrieval, decryption routines, and file patch sequences are identical.
Once installed, these libraries are designed to steal user-provided Cursor credentials and fetch the next valid payload from remote servers, replacing legitimate Cursor-specific code with malicious logic. Additionally, sw-cur takes further steps to disable Cursor’s automatic update mechanism and terminate all Cursor processes. The npm packages then restart the application to allow the tampered code to take effect, enabling malicious actors to execute arbitrary code in the platform’s environment.
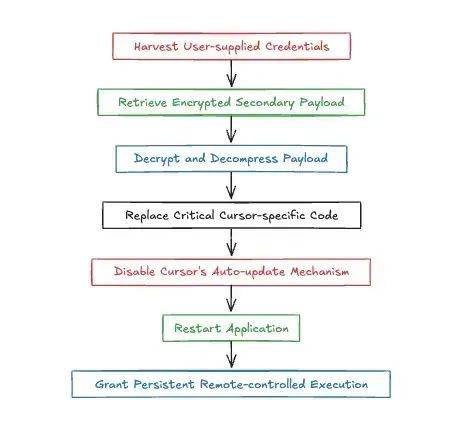
Attack Mechanism
This attack specifically targets the installation of Cursor on macOS systems by modifying internal files like main.js located under the path /Applications/Cursor.app/…, leveraging the trusted runtime environment of the editor to execute code controlled by malicious actors and maintain operation.
“The design of these three packages indicates that attackers deliberately exploit developers’ workflows and the trust boundaries of IDEs to gain long-term access and control. This is an attack on the trust developers place in their coding tools,” Socket advises that any organization suspecting an attack should reinstall Cursor from verified installers, change all affected credentials, and audit source code control and build artifacts for unauthorized changes.
The Cost of Cheap APIs
This type of attack highlights the growing threat of supply chain vulnerabilities, as malicious actors increasingly use harmful patches to attack trusted local software. Boychenko noted that the success of such attacks relies on exploiting developers’ interest in AI and the tendency of some to avoid paying for Cursor AI usage, seeking cheaper access to AI models.
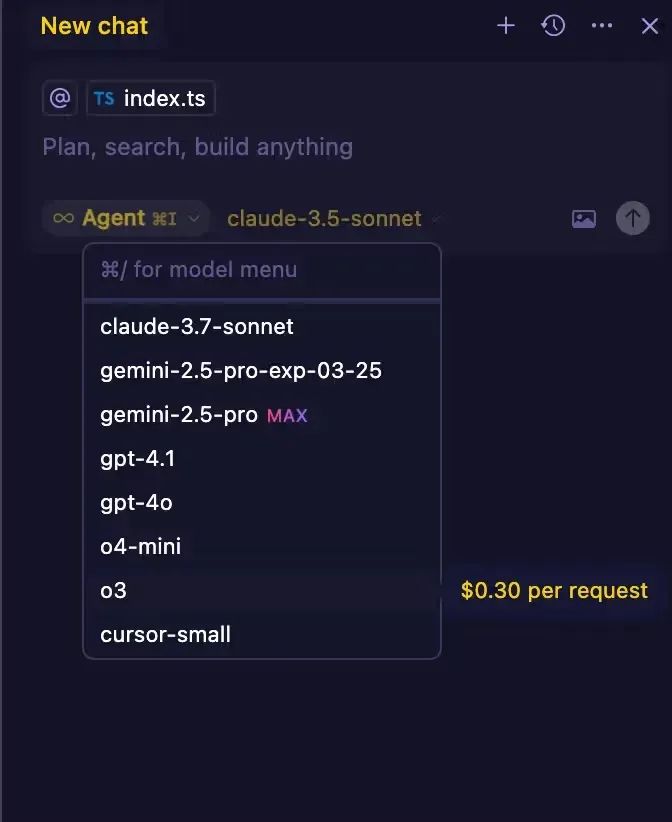
As an AI-centric IDE, Cursor offers tiered access to large language models like Claude, Gemini, and GPT-4, with charges per call for higher models (e.g., OpenAI’s latest inference model o3 charges $0.3 per call). While users can use their own API keys, some may seek cheaper or unofficial integration methods to reduce costs.
“Malicious actors using slogans like ’the cheapest Cursor API’ likely target this group, enticing users with promises of discounted access while quietly deploying backdoor programs,” Boychenko added.
For individual users, the infected IDE poses direct risks of credential theft, code leaks, and potential delivery of further malware. Once malicious actors gain access to Cursor credentials, they can access paid services and, more critically, any codebases the victim has opened in the IDE. As the injected code runs with user permissions, it can execute further malicious scripts or extract sensitive data undetected.
In enterprise environments or open-source projects, the risks multiply. A trojanized IDE on a developer’s computer could leak proprietary source code, introduce malicious dependencies into builds, or serve as a foothold for lateral movement within CI/CD pipelines. The malicious patches disable Cursor’s automatic update mechanism, allowing them to remain active for extended periods.
However, some users have pointed out that “this merely highlights the supply chain risks we all face. Currently, they target those willing to download ’the cheapest API.’ But theoretically, no one can stop someone from packaging malicious code into specific releases of vi/vim/gvim packages.”
The Rise of Malicious Packages
Socket’s findings indicate an emerging trend where malicious actors exploit rogue npm packages to maliciously modify other legitimate libraries or software already installed on developers’ systems. This issue needs urgent attention, as it allows malware to persist even after the malicious library is removed, adding a new layer of complexity that requires developers to cleanly reinstall tampered software.
Socket further explained: “Patch-based intrusions are a new powerful tool in the arsenal of malicious actors targeting open-source software supply chains: attackers do not (or additionally) inject malware into package managers but release seemingly harmless npm packages that rewrite trusted code on the victim’s computer. By operating within a legitimate parent process (IDE or shared library), the malicious logic inherits the application’s trust, allowing it to persist even after the problematic package is deleted and automatically gain any permissions the software has, from API tokens and signing keys to external network access.”
To counter such new supply chain threats, defenders need to flag packages that run post-install scripts, modify files outside of node_modules, or initiate unexpected network calls, combining these flags with strict version pinning, real-time dependency scanning, and file integrity monitoring for critical dependencies.
Alongside the disclosure regarding Cursor, Socket also discovered two additional malicious npm packages: pumptoolforvolumeandcomment and debugdogs, which reportedly deliver obfuscated payloads to steal cryptocurrency keys, wallet files, and transaction data related to a cryptocurrency platform named BullX, targeting macOS systems. The captured data is sent to a Telegram bot.
These two packages were released in September 2024 by a user named “olumideyo,” with pumptoolforvolumeandcomment downloaded 625 times and debugdogs downloaded 119 times.
“‘debugdogs’ simply calls ‘pumptoolforvolumeandcomment,’ making it a convenient secondary infection payload. This ‘wrapper’ model reinforces the primary attack vector, allowing malicious code to spread easily under multiple names without altering the core malicious code,” security researcher Kush Pandya stated. “This highly targeted attack can drain wallets and expose sensitive credentials and transaction data within seconds.”
Comments
Discussion is powered by Giscus (GitHub Discussions). Add
repo,repoID,category, andcategoryIDunder[params.comments.giscus]inhugo.tomlusing the values from the Giscus setup tool.